In 2023, critical vulnerability registrations surged 3 times compared to 2019-2022 average. Although there has been a slight decrease in 2024, the trend persists due to increasing popularity of Linux systems, Kaspersky finds.
Exploits are programs designed to leverage various vulnerabilities in cyberattacks. Latest Kaspersky Security Network data reveals an increase in attacks with exploits against Linux users. The research indicates the peak was in Q4 2023, while overall trend for growth is persisting in 2024, with an insignificant decline in Q1. In January-March 2024, there has been a nearly 130% increase in attacks on Linux users employing various exploits and vulnerabilities compared to the same period last year.
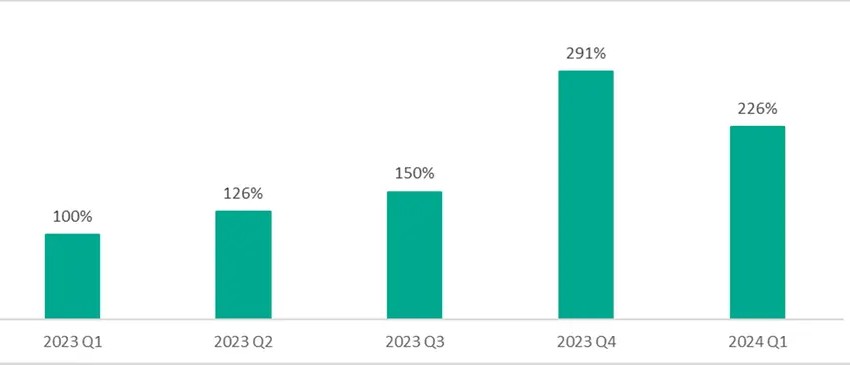
Share of Linux users, protected by Kaspersky solutions and facing vulnerability exploits in 2023-2024. Q1 2023 figures are 100%.
Linux is gaining traction the desktop operating system market. According to Statcounter, its market share has grown, and the number of users increased. “This trend quite accurately explains the growing threat landscape we witness for Linux. In the future, the number of exploits and attacks is likely to grow even more, underscoring the vital need for installation of patches and having a reliable security solution,” says Alexander Kolesnikov, a security expert at Kaspersky. “The greatest value for exploit developers lies in vulnerabilities within software that grant control over a user’s system.”
Critical vulnerability registrations rise over the last four years
Kaspersky recorded a 65% increase in the number of registered CVEs (Common Vulnerabilities and Exposures) over the last four years, from 15,000 in 2019 to 25,000 in 2023. Moreover, during the last year, researchers and companies logged critical vulnerabilities three times more frequently than the research period average. The annual average of critical vulnerabilities registrations from 2019 to 2022 was 413, which spiked to the absolute number of registrations of 1213 in 2023.
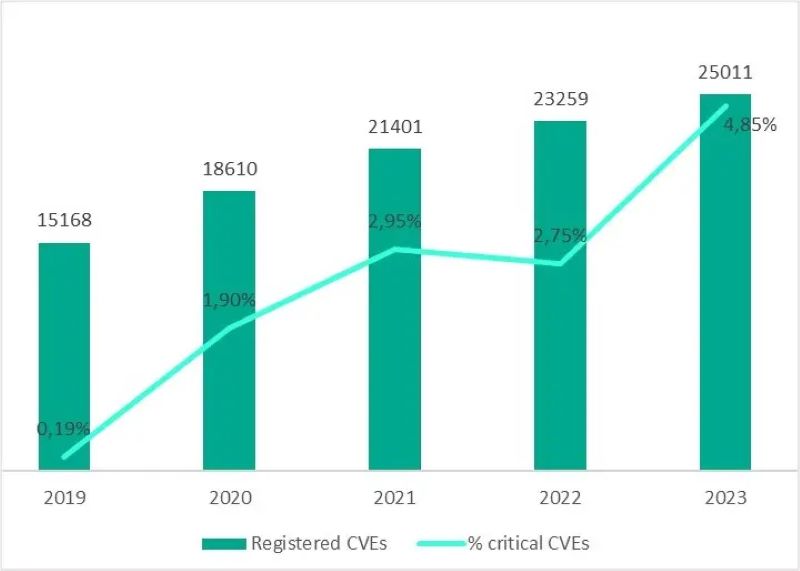
New CVEs with the share of critical vulnerabilities, 2019-2023. Source: cve.mitre.org
To ensure corporate cybersecurity, companies are recommended to follow this advice:
- Thoroughly understand your infrastructure and closely monitor its assets, with particular focus on the perimeter.
- Implement a Patch Management process to detect vulnerable software within the infrastructure and promptly install security patches. Solutions like Kaspersky Next and Kaspersky Vulnerability Data Feed can assist in this regard.
- Conduct regular security assessments to identify and patch vulnerabilities before they become an entry point for an attacker.
- To protect the company against a wide range of threats, use solutions from Kaspersky Next product line that provide real-time protection, threat visibility, investigation and response capabilities of EDR and XDR for organizations of any size and industry. Depending on your current needs and available resources, you can choose the most relevant product tier and easily migrate to another one if your cybersecurity requirements are changing.











