Advanced Persistent Threat (APT) actors are targeting vulnerable remote access services and access control mechanisms like Windows Smart Screen in their attacks leveraging vulnerability exploitation, the latest research by Kaspersky has revealed. Analysis of available data on exploits used in APT attacks in 2023-2024 also shows that office applications like Microsoft Office and WinRAR are frequent targets.
Although APT attacks rarely occur, they pose a significant threat to large corporations. Threat actors usually target specific objectives, and endeavor to remain undetected within the infrastructure for prolonged periods.
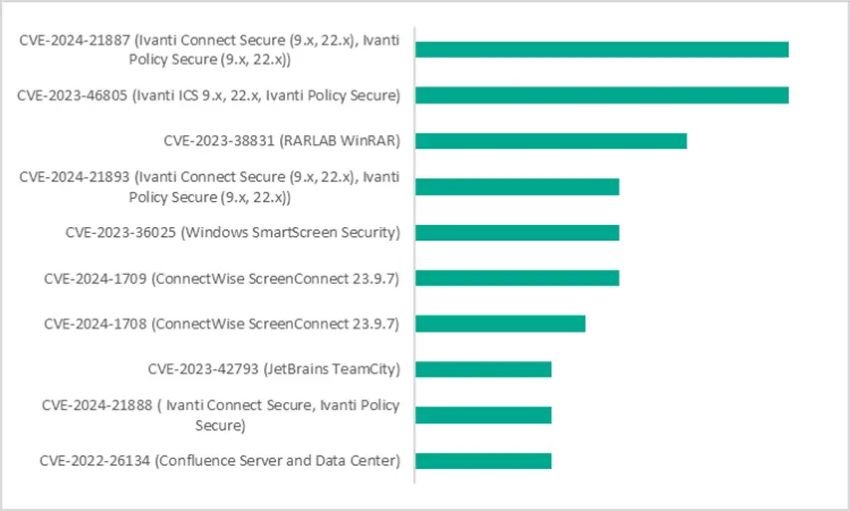
In the first quarter of 2024, the most popular vulnerabilities used by advanced adversaries turned out to be command injection and authentication bypass in Ivanti’s software for IT security and systems management – CVE-2024-21887 and CVE-2023-46805 (Common Vulnerabilities and Exposures) respectively, according to the available data on APT attacks.
Vulnerabilities used in APT attacks in January-March 2024 by the number of attacks
The popularity of CVE-2024-21887 is likely due to its novelty. In targeted attacks, adversaries typically exploit vulnerabilities actively in the first weeks following registration and publication, before companies have had the chance to apply patches. The CVE-2023-46805 vulnerability may be used in conjunction with CVE-2024-21887.
In third place is the vulnerability in WinRAR, discovered in 2023 but still actively used in targeted attacks. It misleads users regarding the nature of the archived file being opened, thereby lowering their vigilance.
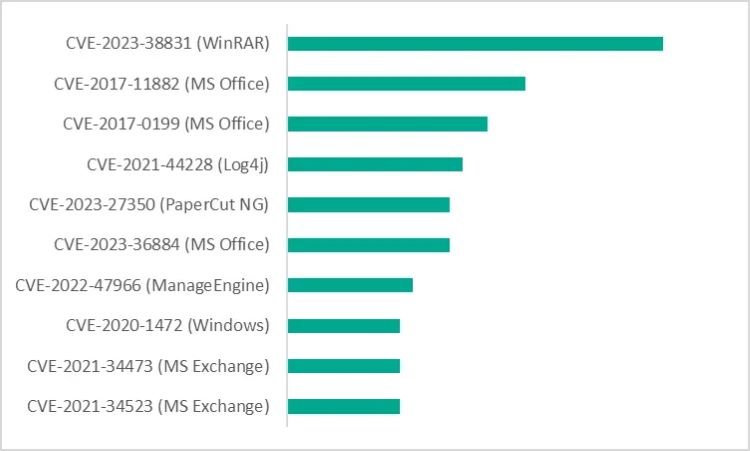
In 2023, the most exploited vulnerabilities in advanced attacks were found to be the ones in WinRAR (CVE-2023-38831), with CVE-2017-11882 and CVE-2017-0199 in the Microsoft Office suite following behind.
Vulnerabilities used in APT attacks in 2023 by the number of attacks
“Interestingly, while exploits for the Microsoft Office suite have traditionally held first place and widely used – due to Windows’ popularity that of its software in the corporate world – the latest snapshot of APT attacks reveals a different trend. Microsoft Office has ceded its leadership to WinRAR exploits,” explains Alexander Kolesnikov, a security expert at Kaspersky.
The analysis was conducted utilizing information from available sources on APT attacks, which leveraged CVEs that have been registered.
To mitigate the risk of advanced attacks, experts advise:
- Thoroughly understand your infrastructure and closely monitor its assets, with particular focus on the perimeter.
- Implement a Patch Management process to detect vulnerable software within the infrastructure and promptly install security patches. Solutions like Kaspersky Next and Kaspersky Vulnerability Data Feed can assist in this regard.
- Conduct regular security assessments to identify and patch vulnerabilities before they become an entry point for an attacker.
- To protect the company against a wide range of threats, use solutions from Kaspersky Next product line that provide real-time protection, threat visibility, investigation and response capabilities of EDR and XDR for organizations of any size and industry. Depending on business’ current needs and available resources, the most relevant product tier can be chosen with easy migration capabilities to another one if your cybersecurity requirements are changing.